Web Dev. Reading List #125
It’s Friday again, and I found some interesting articles for you to read over the upcoming weekend. In projects, developer, manager and product leaders still try to put pressure on the people who work on a task. Somehow they feel relieved, more secure if they do that. On the other hand, the people experiencing the pressure of urgency are struggling massively with it.
The fallacy here is that while the ones spreading the pressure feel better, the people experiencing it usually do a worse job than without the pressure. It leads to more bugs, unstructured work and, in the end, all people involved will suffer from the result. So instead, a team, which includes everyone from a developer to a manager, should focus on the purpose of the work. Give it a try, y’all, and now, enjoy your weekend!
General
- Imagining your future projects is holding you back. Jessica Abel talks about the problem of idea debt, about thinking too much and making too little.
Tools
- Textlint lets you lint document text content using rules you specify. This is cool to check for grammar or formatting problems in Markdown files.
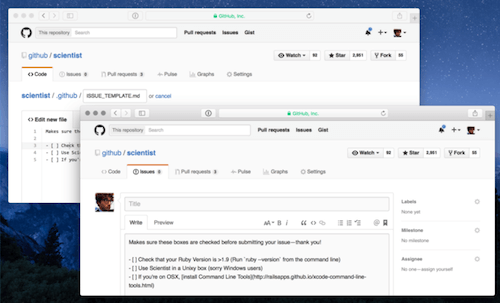
- GitHub now offers templates for issues and pull requests. Oh, and they enabled file uploads as well.
Security
- A bug in
glibchas been disclosed. As it’s a very bad and easy to exploit bug, you should patch every server (and clients) as soon as possible. - Never say “We’ll just use defaults, for now. That password will do, for now.” in the context of security. It’ll be forgotten, and this is the most dangerous threat to your data, giving attackers the possibility to do anything with very little effort. Do you have a VoIP phone with a default password? A WiFi router? Change it to something secure. And please tell your friends and family as well. This is important.
Privacy
- This week, Apple started a new discussion about privacy, encryption and built-in backdoors on their devices. They received an order to build a custom iOS built, signed by Apple, that lacks several security measurements so that the FBI could hack into phone data relatively easily. In an open letter Apple shared why they declined to do so. Luckily, a lot of companies seem to agree with Apple, and I hope we can find a good way to protect our privacy, and with that, our personal security. Because, as we all know, even if such a backdoor is kept secure, no one could assure that this piece of software won’t get stolen and abused by someone who shouldn’t have access to it.
Web Performance
- Rachel Andrew wrote a great guide on how you should start to make a plan for the transition of web projects to HTTP/2. As the switch should be well planned, it’s a great idea to establish a process to migrate seamlessly and, for now, generate assets and pipelines for both, HTTP/1.1 and HTTP/2, so that a switch is easy.
JavaScript
- So, this is nothing ground-breaking but if you ever wondered about a good cross-browser way to check if the document has loaded in pure JavaScript, this code snippet is for you.
- The still relatively new ESLint has been released in version 2.0. It breaks at some point with v1.x but now comes with an auto configuration feature and also introduces code path analysis.
- Hunt by Jeremias Menichelli is a JavaScript library that detects if an element becomes visible/invisible and acts on these events, by adding or removing classes, for example. This makes it a great tool to animate elements on scrolling and other interactions.
CSS / Sass
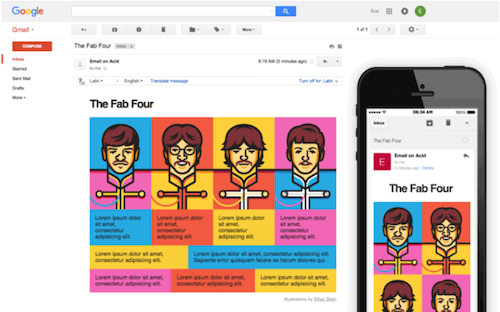
- Rémi Parmentier shares a clever way to build flexible, responsive containers without media queries which makes the technique a good option for email newsletters.
- This huge Codepen gives you an interactive playground for Flexbox properties and values so you can try out what you need for your use case.
- To be honest, despite the usual
currentColoruse case for inheriting the current color into an SVG element, there are not a lot of ressources that explain how you can use this value. But this example shows you how to usecurrentColorfor colored elements with pseudo-element arrows in it in a clever way. - Michael Scharnagl shares how you can use the new custom properties (also known as CSS variables) to build a theme switcher for your project.
Work & Life
- Trying to create a sense of urgency almost always backfires. So why not foster a sense of purpose instead, which is much better for our brains and our health?
- As a founder of a company, your most important skill should be hiring people. Moritz Plassnig from Codeship tells us why it’s so important to build a great team if you want to succeed with your product.
Going Beyond…
- Last week, I wrote that most of the time the software we write is not critical to people. But what happens if it is? For example, if you sell a smart thermostat and due to a bug in its software the heating is disabled entirely with no option to fix it yourself? This happened to Nest users, showing the problems of ‘smart’ devices that control critical things in our lives.
And with that, I’ll close for this week. If you like what I write each week, please support me with a donation or share this resource with other people. You can learn more about the costs of the project here. It’s available via E-Mail, RSS and online.
Thanks and all the best, Anselm
Further Reading
- P Vs. NP: The Assumption That Runs The Internet
- Why Passphrases Are More User-Friendly Than Passwords
- The Current State Of Authentication: We Have A Password Problem
- Obfuscating Blacklisted Words In WordPress With ROT13


 See User Testing Live
See User Testing Live Celebrating 10 million developers
Celebrating 10 million developers



 Custom Web Forms for Angular, React, & Vue. Your backend.
Custom Web Forms for Angular, React, & Vue. Your backend.

